Here’s what we look for in trustworthy technology: end-to-end encryption, open source code, and cross-platform support. Here we dive into the importance of end-to-end encryption and why we recommend groups use the open-source, end-to-end encrypted, and cross-platform app Wire instead of the proprietary and probably-not really end-to-end encrypted Zoom whenever possible for conference calls (especially when privacy matters). Signal is also really good too, but doesn’t do conference calling.
We still rely on Zoom for conference calls, but we now consider them to be more or less public meetings rather than a secure channel. Why?
Let’s start by clarifying the phrase “End-To-End Encryption”—this is a technical term meaning a message is scrambled so that it can only be read by the endpoints of a conversation. But here’s where confusion comes in—what are the endpoints? Are they just you and your friends? Or is the server an endpoint too? It depends on the application. As an example, HTTPS (which secures communications between you and the servers hosting the webpages you visit) is encrypted so that only you and the server can decrypt the content of the webpages. Signal, a secure instant messaging app tied to your smart phone, encrypts messages so that only you and your friend that you are messaging can read your messages. In both cases, only the people or entities that you could imagine needing to know the information are able to decrypt encrypted information. This is the heart of end-to-end encryption. Please check out our post on Direct Encryption for more details on end-to-end encryption.
We are concerned that the fancy webconferencing app Zoom could be exploiting this confusion to exaggerate the security of their platform. The best case scenario is that Zoom does what ProtonMail does: manage the keys needed for encryption for you. The reality is probably worse, since the few technical details Zoom provides do not describe enough technical components to actually achieve end-to-end encryption. Their own web portal’s menu indicates that they are not providing end-to-end encryption, but in-transit encryption, that is, encrypting messages between the participants in a conversation and Zoom’s servers: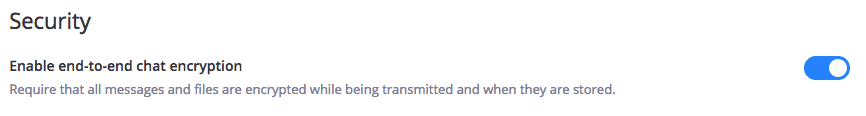
That is, is appears Zoom considers their own servers an “end”. This language is repeated in their security white paper. And because the source-code for Zoom is not public, there is no way to verify any of their claims. Even if we give Zoom the benefit of the doubt, and have faith that they are providing end-to-end encryption, the existence of such a toggle in a web menu gives the web server—that is, Zoom—the ability to flip this switch without your knowing. We’re not saying we know for a fact that Zoom would fail to play nice and violate your privacy. But we are saying that your privacy relies entirely on Zoom to play nice. Most importantly: ask yourselves what Zoom would do if asked to meet national security or law enforcement requirements?
The world of digital security changes rapidly. We started using Zoom last year to do remote trainings and conference calls when it looked like there was no reliable, secure option for group calls. Zoom works really well in terms of call quality and participant management features, but the reality is that there are better security-focused options now, and we want to direct people toward using these—Signal and Wire are our top choices—whenever possible.
Zoom isn’t the worst in terms of security (not as bad as cellphones or some random free conference call service), and Wire can’t do large conference calls, so there are still some use cases for it. Instead of giving up on security, it can help to think of the various options as tiers of encryption:
Tier 1 (top shelf, best possible security) uses truly end-to-end, Direct Encryption. Private conversations can only be eavesdropped on by breaking into one of the participants’ devices. Wire and Signal meet this standard, and are also open source, so their security claims can be thoroughly verified. If Zoom does this for 1-on-1 calls, as they claim, they could switch it off anytime–it’s a setting that zoom customers/administrators can change via the administrator panel at zoom.us—so a zoom employee could do the same thing. This is a pretty terrible implementation of end-to-end encryption, so we don’t count it as Direct Encryption, where *only* you and your friends control encryption keys.
Tier 2 (less than ideal but still hard for some adversaries to break) is the sort of “in transit” encryption Zoom uses for group calls where comms are encrypted from participants’ devices to Zoom’s server, mixed, encrypted again then sent out to all participants’ devices. Breaking this would likely require Zoom’s active co-operation, most likely obtained via a warrant or National Security Letter.
Tier 3 (not at all good, open to multiple adversaries including private security) is plain old cell phone encryption—governments can relatively easily ask cell phone companies for access to their networks (and to break encryption done by the cell phone company)—worse yet, cell site simulators (“Stingrays”) can force phone network security down from 4G to 3G, weakening encryption enough for anyone with access to a Stingray to break (local cops, very probably corporate security).
This is why CLDC is recommending Wire–it’s open source, does end-to-end encrypted 1-on-1 video, and allows up to 10-people in end-to-end voice conference calls. Get it here.
We’re happy to help you and your org get set up with Wire and other trustworthy tech, and in the meantime there’s also a nice beginners guide to Wire.